
Tesla Hackers Are Stealing Cars by Making Their Own Keys
With space-age steps to make their electric vehicles (EVs) even more advanced, Tesla may have handed hackers and thieves every tool they need to steal the cars fast. There are a few ways to access your Tesla, including your phone or an NFC card on your person. However, these new measures have their own susceptibilities that could leave Tesla EVs vulnerable to theft.
What are NFC cards?
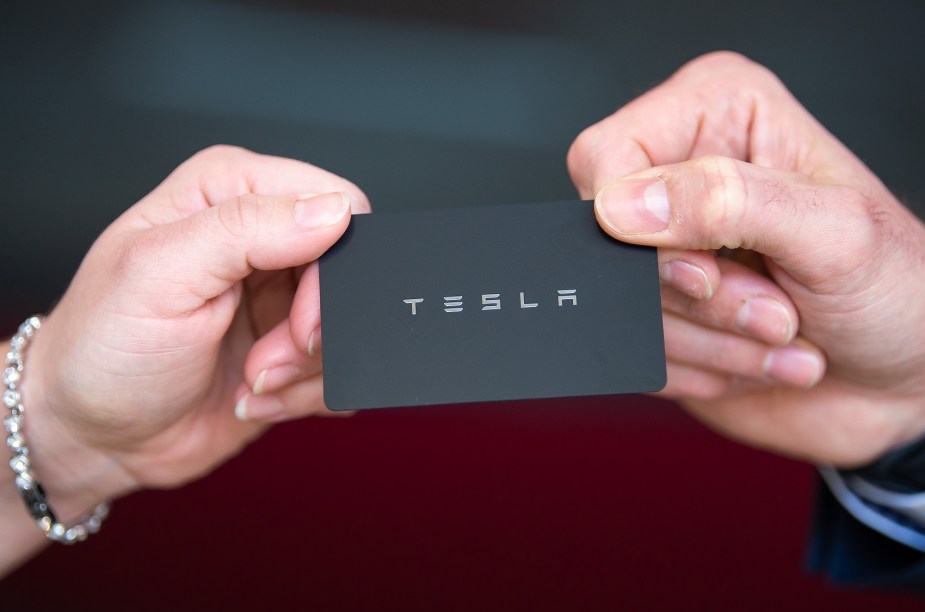
Near field communication cards, or NFC cards, facilitate communications between two devices, like a door lock and a card. The technology allows Tesla users to unlock their vehicles with a card instead of a key.
Are Tesla cards NFC?
Tesla’s access cards use NFC technology. Tesla intended the cards to give owners an alternate option for vehicle security. As of now, owners can unlock their cars with an NFC card, a mobile phone app, or a key fob.
How do NFC cards work in Tesla EVs, and are they susceptible to Tesla hackers?
At first, users had to introduce the NFC cards to the door and then place the card on the center console to start and drive the car. After a recent update, though, owners have a 130-second period after using the NFC card to unlock the vehicle in which they can drive it. However, the 130 seconds might be too general and leave the car vulnerable to Tesla hackers, according to Wired.

How can Tesla hackers use NFC cards to steal Teslas?
Given the 130-second period following NFC card unlocking, a Tesla is ready to drive. However, according to Wired, that period allows the car to accept new keys. That means savvy potential Tesla hackers could make their own keys to drive off with a Tesla.
Martin Herfurt, an Austrian security professional, suggests that the 130-second period is “too general” and allows the “enrolling of a new key.” According to Herfurt, the period will enable devices using Bluetooth low energy (BLE) to communicate with the cars. Wired says that Herfurts own app, Teslakee, uses the digital language VCSec to receive BLE communications. Using this technology, anyone can enroll a key during the 130-second period.
Which cars are at risk?
As of now, Herfurt suggests that he’s tested the concept with both the Tesla Model 3 and Model Y. However, he believes that the Model S and Model X will be vulnerable as well, given the BLE applications of both vehicles. So it stands to reason that every Tesla might be susceptible to the practice.
How can you prevent Tesla hackers from stealing your Tesla using this practice?
While the practice seems scary, there is some good news. First, the method isn’t exactly practical. It requires the NFC cardholder to unlock the car and then the would-be thief to gain control of the car during the 130 seconds. It seems like an impractical way of stealing an EV.
However, Wired makes it sound as though Tesla is unlikely to remedy the problem. Instead, drivers can set up Pin2Drive, to provide a simple layer of security for your Tesla. Furthermore, you can use your key fob if you feel uncomfortable using the NFC technology.
Scroll down to the following article to read more about Teslas!



